 **)**
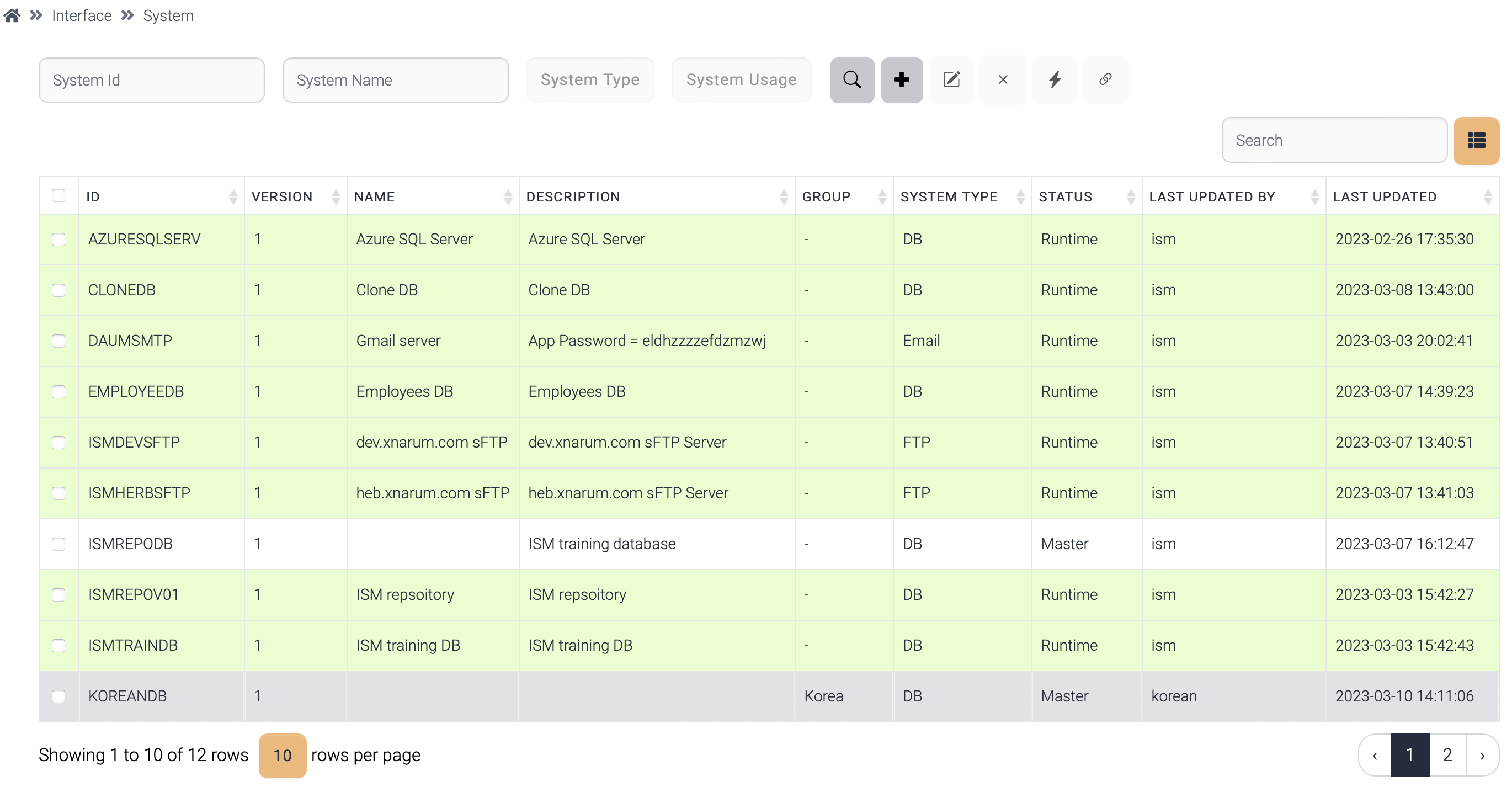
System information is loaded from database, converted into an object, and saved into a memory cache. If the system is used by the running instances, the object is replaced with the new one.
**)**
System information is loaded from database, converted into an object, and saved into a memory cache. If the system is used by the running instances, the object is replaced with the new one.
 **)**
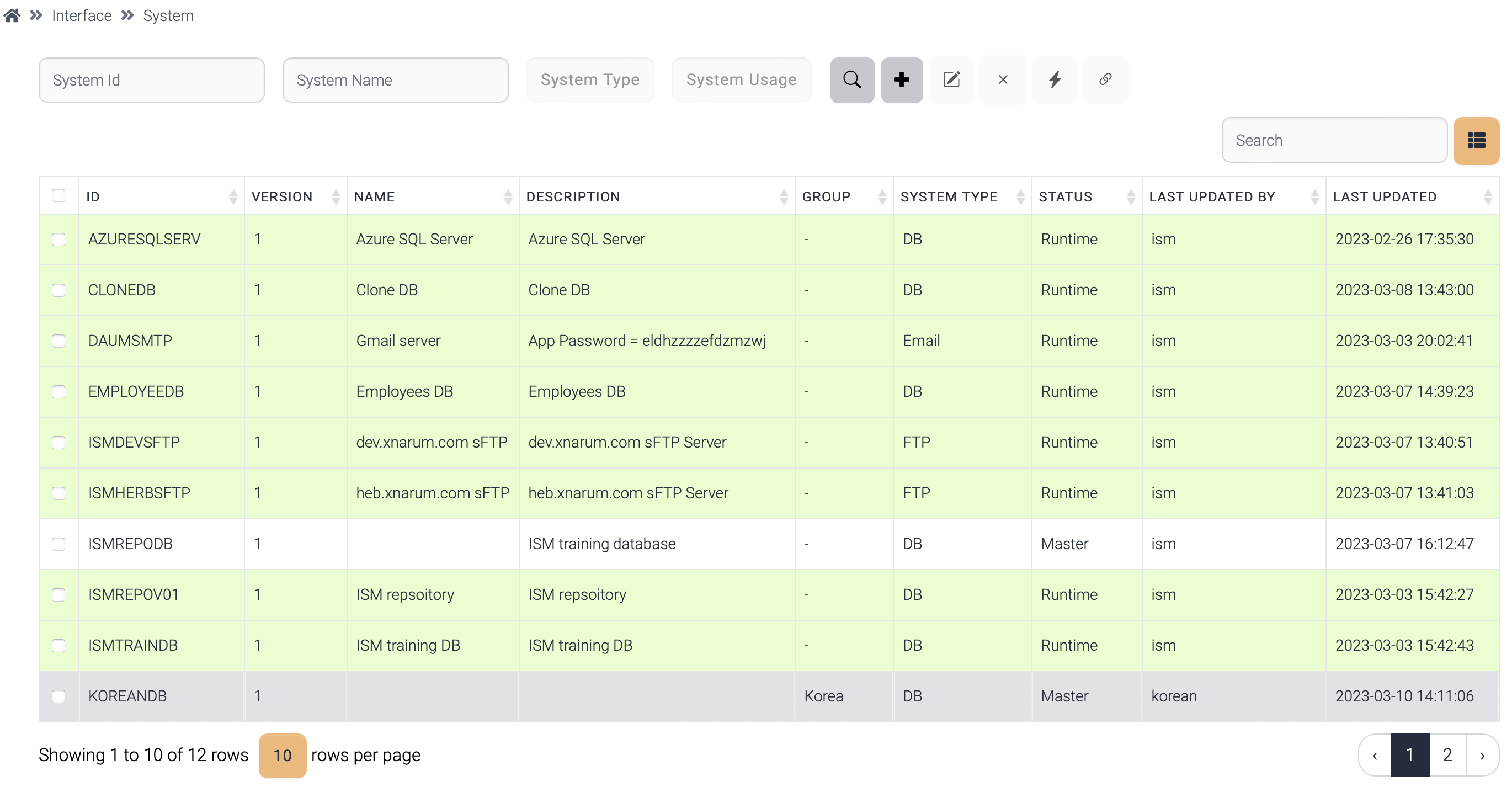
If a system is used by any flow, this system is displayed in green background.
The hierarchies of the items are these.
· Flow > system
· Flow > data structure > field group > field
!\[Graphical user interface
Description automatically generated]\(
**)**
If a system is used by any flow, this system is displayed in green background.
The hierarchies of the items are these.
· Flow > system
· Flow > data structure > field group > field
!\[Graphical user interface
Description automatically generated]\(jdbc:oracle:thin:@localhost:1521/service\_name
jdbc:oracle:thin:@localhost:1521:SID
| | Sqlserver | jdbc:sqlserver://localhost:1433;databaseName=database\_name | | Postgresql | jdbc:postgresql://localhost:5432/database\_name | | DB2 | jdbc:db2://localhost:446/dbname | | DB2 AS 400 | jdbc:as400://hostname/default-schema | Click test button, then the connection information can be verified. !\[Graphical user interface, application Description automatically generated]\(File transfer protocol
FTP, sFTP, SCP, FTPs
| | User | File user | | Password | User password | | Private key | Private key for sFTP or FTPS connection | | Passphrase | Passphrase to access private key | (s)FTP connection can be verified like database. · Creating a private key Run this command at the server. If you want a passphrase, enter passphrase otherwise press enter. $>ssh-keygen -f my-private.key !\[Diagram Description automatically generated with low confidence]\(JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. This information can be verified and trusted because it is digitally signed. JWTs can be signed using a secret (with the HMAC algorithm) or a public/private key pair using RSA or ECDSA.
Although JWTs can be encrypted to also provide secrecy between parties, we will focus on signed tokens. Signed tokens can verify the integrity of the claims contained within it, while encrypted tokens hide those claims from other parties. When tokens are signed using public/private key pairs, the signature also certifies that only the party holding the private key is the one that signed it.
| | ---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | (From
| Property | Description |
|---|---|
| User | User id |
| Password | Password |
| User Field | Field name of the user field |
| Password Field | Field name of the password field |
| Content Type | Content type of the authentication request
|
| Authentication URL | Endpoint for the authentication |
| Property | Description |
|---|---|
| User | User id. Optional |
| Password | Password. Optional |
| Class Name | The java class which generates authentication information. |
| Property | Description |
|---|---|
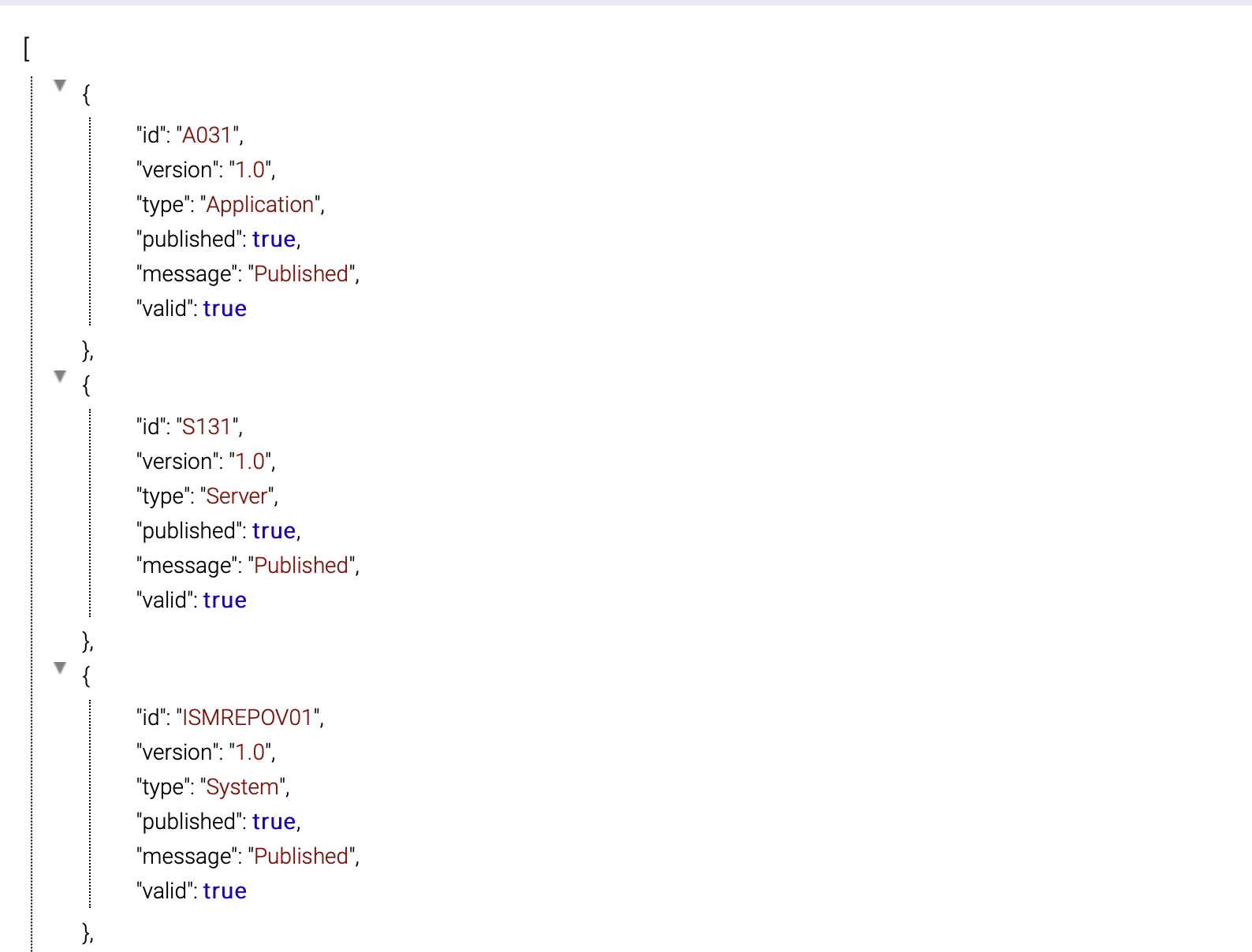
| Host | Target host |
| Port | Listening port of the target server |
| Length Type | Length field type · Short - 2 bytes length · Integer - 4 bytes length · Character - Stringified length Short/Integer length is binary data and Character expresses length in character. ex) 00001200 - Length of the data is 1200 bytes |
| Size of Length | Size of length field
|
| Header Length | The length of header data. Header data contains meta data of the message like followings: · Length · Message Type · Transaction ID |
| Length Offset | The position of the length field. Mostly the first few bytes are the length and offset is 0. |
| Is Total Length? | Does the value of the length field include length field? · Yes - length field is part of the length. · No - length field is not part of the length. |
| Property | Description |
|---|---|
| SMTP Server | SMTP Host. Main and backup, if exists. |
| Port | SMTP Port. Mostly used ports are these: 25 - non-SSL port 465 - SSL port |
| Use SSL? | If use ssl, SSL modules are used to connect SMTP server. |
| User ID | User id of the email server. Mostly id is the email address of the sender. |
| Password | Password of the email sender. |
| Property | Description |
|---|---|
| Host | MQ Queue manager host |
| Port | MQ Listener port |
| Queue Manager | Queue Manager name |
| Queue Name | Request queue |
| Channel Name | SVRCONN name |
| Reply Queue manager | Reply queue manager |
| Reply Queue Name | Reply queue name |
| Character Set | Character encoding. Necessary when conversion is required. EBCDIC <-> UTF8 |
| User | User id of the host which MQ is running on |
| Password | Password |